I'll outline 15 defenses against DDoS attacks in this post.
The two main categories of DDoS attacks are resource exhaustion attacks and bandwidth exhaustion attacks. You can effectively stop these two types of attacks by following the instructions provided in this article.
- An ACL (access control list) is placed on the firewall server to prevent access from those IP addresses if the attack is limited to a small number of computers and you have determined the IP addresses associated with those computers. Alter the web server's IP address if you can, but this will become invalid if the attacker uses your newly configured IP address to resolve DNS queries.
- Consider blocking the IP address from that nation, at least temporarily, if you are certain that the attack originates there.
- keeping an eye on the coming network traffic. You can then monitor the visitor's exception and examine the log and source IP to learn more about who is accessing your network. An attacker could test the resilience of your network with a limited number of attacks prior to launching a larger campaign.
- Purchasing additional bandwidth is the most financially burdensome (and efficient) way to counteract bandwidth-hungry attacks.
- Additional options include the use of multiple servers, high-performance load balancing software, and deployment in various data centers.
- the use of load balancing for DNS protection in addition to other resources, including the web.
- Maximize the web server load capacity by making optimal use of available resources. For example, you can use Apache to install the Apachebooster plug-in, varnish, and nginx integration to handle an unexpected spike in traffic and memory footprint.
- the defense against DNS DDOS attacks through the use of highly scalable DNS devices. Think about the Cloudflare commercial solution, which can protect DNS or TCP/IP from layer 3 to layer 7 against DDOS attacks.
- Give the firewall or router permission to spoof IP addresses. The CISCO ASA firewall offers more convenient function configuration than the router. In ASDM (Cisco Adaptive Security Device Manager), enable this feature by selecting "Firewall" under "Configuration," then "anti-spoofing," and finally clicking Enable. In order to stop IP spoofing, you can also use the router's ACL (access control list), which is applied to the Internet interface after first being created by the network.
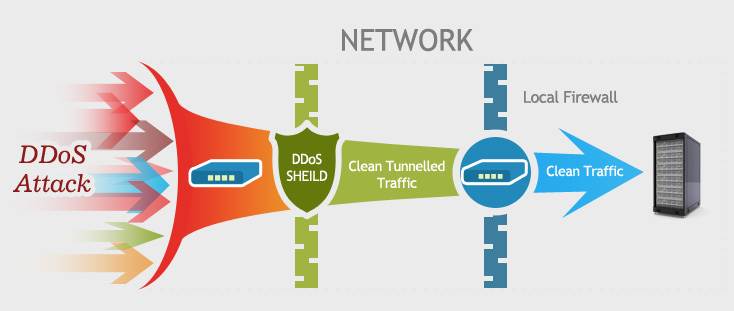
- utilizing outside services to safeguard your website. Numerous businesses offer high-performance basic network facilities to help you fend off denial-of-service attacks. The monthly cost of the line is only a few hundred dollars.
- To prevent DDOS attacks that cause resource exhaustion, pay close attention to the server's security configuration.
- Expert opinions should be heard in order to prepare for potential attacks and how to handle emergency programs.
- keeping an eye on online and network traffic. Multiple analysis tools, like Statcounter and Google Analytics, can be configured to provide you with more information and a better visual representation of the traffic pattern changes.
- to defend DNS in order to fend off attacks that amplified DNS.
- Turn off ICMP on the router. Only open ICMP when testing is necessary. When configuring the router, the following techniques are also taken into account: SYN threshold, disable ICMP and UDP broadcast, flow control, packet filtering, half-connection timeout, garbage packet discard, source forged packet drop, and so on.

Post a Comment
0Comments